Key Takeaways
- Blockchain digital identity shifts control from central authorities to users.
- Over 1.1 billion people worldwide lack formal identity, limiting economic access.
- Self-sovereign identity (SSI) uses verifiable credentials and decentralized identifiers (DIDs).
- Adoption reduces data breach exposure and streamlines verification processes.
- Standards like W3C DIDs and Verifiable Credentials ensure interoperability.
Blockchain digital identity is a decentralized approach to managing personal identifiers using distributed ledger technology. It enables individuals to control their own identity data without relying on centralized authorities.
What Is Blockchain Digital Identity?

The current digital identity landscape leaves users with little say over how their personal information is stored, shared, or monetized. Centralized databases operated by governments, banks, and social media platforms become attractive targets for attackers. A single breach can expose millions of records, as illustrated by the more than 2.6 billion records compromised in global data breaches in 2023 alone, according to the London Blockchain Conference. This technology offers an alternative model built on cryptography, distributed consensus, and user-centric design.
Definition and Core Principles
This system manages identity attributes through a decentralized network, giving users ownership of their credentials. Instead of storing data on a company’s server, claims such as name, date of birth, or professional certifications are cryptographically secured and shared only with explicit consent. This model is often called self-sovereign identity (SSI). Its core principles are:
- Decentralization – no single entity controls the identity repository.
- User consent – data sharing requires explicit permission from the identity holder.
- Minimal disclosure – only the necessary attributes are revealed (e.g., proving age without sharing birth date).
- Interoperability – credentials work across different platforms and jurisdictions.
How It Differs From Traditional IAM
Traditional identity and access management (IAM) relies on central authorities to issue and validate credentials. Users create multiple accounts, each siloed within a service’s database. By contrast, this approach enables a portable, user-held credential that can be verified anywhere. The blockchain acts as a public, tamper-evident ledger for verifying the authenticity of credentials without storing personal data on-chain. This eliminates the vulnerabilities tied to honeypot databases.
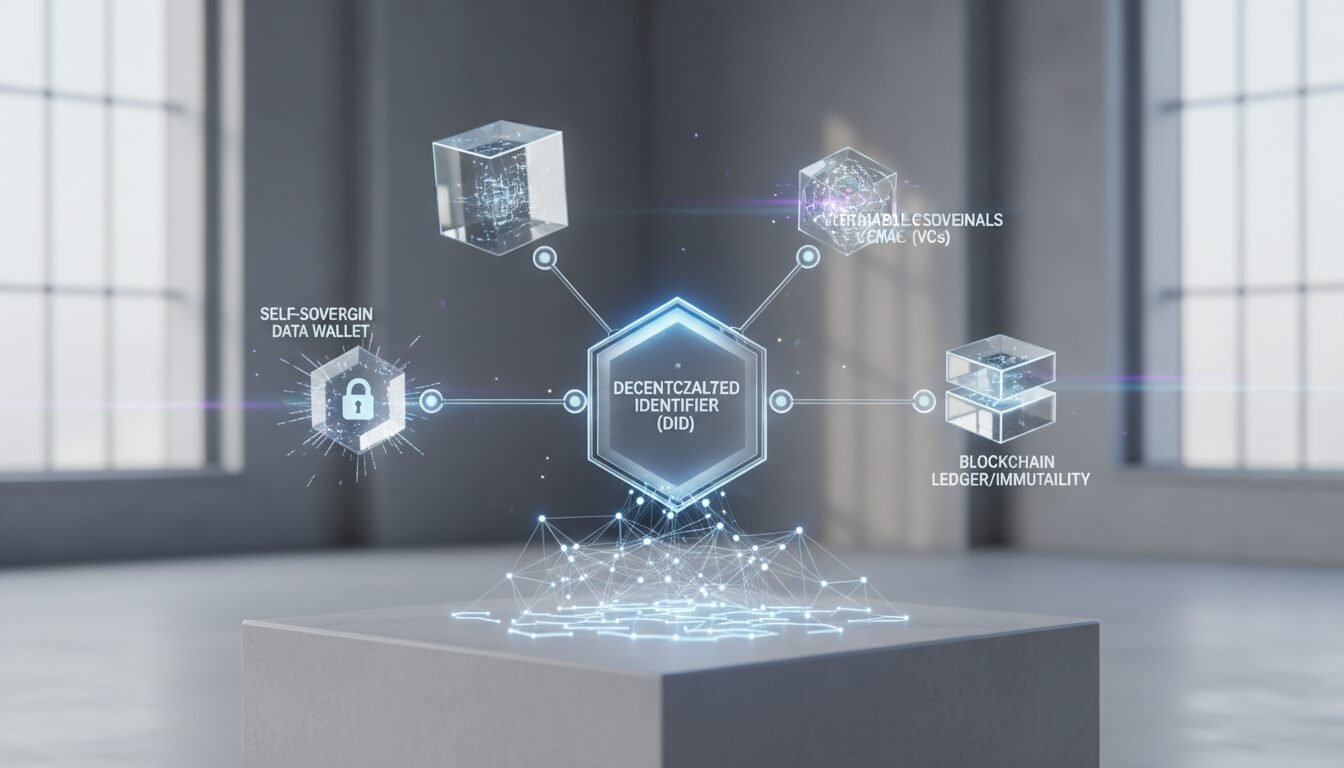
Components: DIDs, Verifiable Credentials, and Wallets
A typical stack includes:
- Decentralized Identifiers (DIDs) – globally unique, persistent identifiers that do not require a centralized registration authority. They are standardized by the W3C.
- Verifiable Credentials (VCs) – tamper-proof digital statements issued by a trusted party (e.g., a university issuing a degree).
- Digital Wallets – applications where users store DIDs and VCs. Examples include the Truvera Wallet from Dock and the Kinexys Digital Identity solution by J.P. Morgan.
How Traditional Identity Systems Fail Users

Before examining the benefits, it’s useful to understand the structural weaknesses of current identity frameworks. Centralized systems create security, privacy, and inclusivity problems that this technology can address.
Data Breaches and Centralized Vulnerability
Central databases remain prime targets for cybercriminals. In 2023 alone, over 2.6 billion records were compromised worldwide. Each breach exposes sensitive personal data, leading to identity theft and financial fraud. The cost of a single breach now averages millions of dollars in fines and remediation, especially under regulations like GDPR. This decentralized approach dissolves this honey pot by storing only cryptographic proofs on-chain while keeping actual data in user-controlled wallets.
Exclusion: 1.1 Billion Without Official ID
According to Consensys, approximately 1.1 billion people worldwide do not have a way to claim ownership over their identity. The World Economic Forum estimates that over 850 million lack any legal identification. This exclusion blocks access to banking, education, and government services. A decentralized identity system can onboard individuals using biometrics or community attestations, creating a trusted digital presence without a national ID.
Friction and Repetitive Verification
Users today juggle dozens of usernames and passwords, repeatedly submitting the same documents to different services. This friction wastes time and increases abandonment rates for businesses. The solution enables reusable verified credentials: once a user proves their KYC details to one financial institution, they can consent to reuse that attestation elsewhere without starting from scratch.
Core Components of Blockchain-Based Identity
Understanding the technical building blocks clarifies why this model represents a fundamental shift.
Decentralized Identifiers (DIDs) and DID Documents
A Decentralized Identifier (DID) is a new type of URI that associates a DID subject with a DID document, enabling trustable interactions via cryptography. DIDs are fully under the control of the individual. They are resolved to DID documents that contain public keys, service endpoints, and other metadata. Unlike email addresses or usernames, DIDs are not reassigned or owned by any provider. The W3C DID Core Specification defines a universal framework that over 80 organizations have contributed to.
Verifiable Credentials and Zero-Knowledge Proofs
Verifiable Credentials (VCs) are the digital equivalent of physical certificates. They carry cryptographic proofs signed by the issuer. An essential evolution is the integration of zero-knowledge proofs (ZKPs), which allow a holder to prove a claim (e.g., “I am over 18”) without revealing the underlying data (the exact birth date). ZKPs minimize data exposure and address one of the long-standing privacy concerns in digital identity.
Digital Wallets and User Control
The user experience revolves around a digital wallet that stores DIDs and VCs. Wallets can be mobile apps or browser extensions. Products like Truvera Wallet by Dock offer biometric-bound credentials, ensuring that the person presenting the credential is the one who received it. This prevents credential sharing and adds a physical layer of security. Users decide which credentials to share, with whom, and for how long.
Real-World Use Cases

The technology is moving beyond pilots into production across multiple sectors.
Financial Services and KYC Compliance
Banks and fintechs spend heavily on Know Your Customer (KYC) processes. With reusable credentials, a customer verified by one institution can share that attestation with another, cutting onboarding time from days to minutes. Kinexys by J.P. Morgan is exploring this model to streamline institutional client onboarding. A 12.9% CAGR growth in the identity and access management market, reported by NEC, underscores the industry’s appetite for innovation.
Education and Professional Credentials
Universities and certification bodies can issue diplomas as VCs. Graduates hold these in their wallets and share them with employers instantly. No need to contact registrars or wait for paper transcripts. Dock’s Truvera platform enables this with standards-based credentials that are valid globally. This reduces fraud, as anyone can cryptographically verify a credential’s authenticity against the blockchain.
Healthcare and Vaccination Records
During the COVID-19 pandemic, digital vaccination passes highlighted both the need for verifiable health credentials and the privacy risks of centralized databases. This approach can place immunization records in the user’s wallet, with the ability to present only the relevant status without leaking other health data. This model can extend to prescriptions, insurance eligibility, and clinical trial consent.
Combating Deepfakes and Synthetic Identity Fraud
Synthetic identity fraud—combining real and fabricated information to create a new identity—is a growing concern, costing financial institutions billions annually. By anchoring a biometric-bound credential to a decentralized identifier, it becomes much harder for attackers to fabricate identities. The tamper-evident nature of blockchain means any alteration of the underlying attestation is immediately detectable. This is an emerging use case that goes beyond traditional identity verification, and it illustrates the unique angle that this technology brings to fraud prevention.
Pros and Cons
Pros
- Enhanced Privacy: Users control what data is shared and with whom through minimal disclosure principles
- Reduced Breach Risk: No central honeypot database means attackers can’t compromise millions of records at once
- Cost Efficiency: Reusable credentials eliminate repetitive verification processes, cutting operational costs
- Global Inclusion: Provides identity solutions for the 1.1 billion people without formal identification
- Interoperability: W3C standards ensure credentials work across different platforms and jurisdictions
Cons
- Key Management Burden: Users must secure their private keys or risk losing access to all credentials
- Scalability Challenges: Public blockchains can be slow and expensive during network congestion
- Regulatory Uncertainty: Compliance requirements vary by jurisdiction and are still evolving
- User Experience Complexity: The technology requires education and may intimidate non-technical users
- Recovery Difficulties: Lost keys mean lost credentials unless backup mechanisms are implemented
Benefits for Enterprises and Individuals
Adopting this approach yields measurable improvements in security, cost, and user experience.
Enhanced Privacy and Data Portability
Users gain true data portability, meaning they can take their identity information from one service provider to another without friction. The self-sovereign model ensures that no personal identifiable information (PII) is stored on the ledger. Only the cryptographic proof resides on-chain, while the actual data stays in the wallet. This aligns with GDPR requirements for data minimization and right to portability.
Reduced Verification Costs and Time
Manual document checks are expensive. A reusable digital identity eliminates repetitive verification steps. Early adopters report significant efficiency gains, though specific percentages vary by implementation. For IoT scenarios, Consensys notes that 22 billion internet-connected devices are expected by 2025. Managing identity for these devices at scale is only feasible with a decentralized, automated system.
Improved Security and Anti-Fraud
Because there’s no central repository to attack, the risk of mass data leaks diminishes. Each credential is individually encrypted and stored on the user’s device. Even if a verifier’s system is compromised, at most a single shared attribute is exposed, not an entire database. This drastically limits the blast radius of any breach.
Challenges and Limitations
Despite its promise, adoption is not without hurdles.
Scalability and Performance
Public blockchains like Ethereum have limited transaction throughput. Storing identity operations on-chain can be costly during network congestion. However, Layer‑2 solutions and purpose‑built chains (e.g., Hedera, Polygon ID) offer higher throughput at lower costs, making frequent credential issuance viable.
Regulatory Uncertainty
Different jurisdictions have varying rules for digital identity. The eIDAS 2.0 regulation in the European Union is advancing a framework for trusted digital identities, but global harmonization remains a work in progress. Organizations must navigate a patchwork of compliance requirements, which can slow down cross-border deployments.
User Experience and Key Management
Self-sovereign identity shifts the burden of securing private keys to users. Losing a master key means losing access to all linked credentials. Wallet providers are addressing this with social recovery mechanisms, biometric backups, and hardware security modules. Still, the industry must solve user-friendly key recovery to achieve mass adoption.
Implementation Guide for 2026
For organizations looking to deploy a solution, a phased approach reduces risk.
Step‑by‑Step Implementation Process
- Assessment: Identify the use case (e.g., employee credentials, customer KYC, student diplomas). Map existing identity data flows.
- Standard Selection: Choose appropriate standards – W3C DIDs, Verifiable Credentials, and optionally OIDC4VC for web integration.
- Blockchain Platform: Select a network that balances security, cost, and performance. Public options include Ethereum with Layer‑2, Hedera, or Cheqd. Private/consortium chains (e.g., Hyperledger Indy) also exist.
- Wallet Integration: Embed a white-label wallet into your application or use an SDK like Truvera from Dock.
- Issuer Setup: Configure the entity issuing credentials. This involves generating a DID for the issuer and anchoring it on-chain.
- Pilot Testing: Run a limited deployment with real users, gathering feedback on UX and security.
- Governance Framework: Establish rules for credential issuance, revocation, and trust anchors. Align with initiatives like the Trust over IP Foundation.
Choosing Between Public and Permissioned Blockchains
Public blockchains offer maximum transparency and security but may expose metadata patterns. Permissioned/consortium chains provide more control over who can operate a node, which may be preferred for enterprise or government use. Hybrid architectures are emerging where personal data stays off‑chain and only proofs are anchored on a public ledger.
Integrating with Existing IAM Systems
Organizations don’t need to rip out their existing IAM. This technology can be phased in via bridges: traditional OAuth/OpenID Connect federations can coexist with DID‑based authentication. Okta, for example, is exploring how decentralized identity can complement its existing workflows, as discussed in their whitepaper Practical Thoughts on Blockchain and Identity.
The Future of Decentralized Identity: Beyond 2026
The convergence of AI, IoT, and Web3 will accelerate the need for trusted, autonomous identity layers. This technology is poised to become the backbone of digital trust.
AI Agents and Machine Identity
As AI agents perform tasks on behalf of humans, they need verifiable identities. Dock’s Know Your Agent (KYA) concept ensures every AI-driven action is authentic and auditable, tying a DID to an agent’s behavior. This extends identity management beyond people to the machine economy, which according to Consensys will include over 22 billion connected devices by 2025.
Decentralized Social Media and User-Controlled Data
Web3 social platforms are experimenting with on‑chain reputation. Instead of usernames tied to a corporate database, users can present a DID that aggregates verifiable achievements, community memberships, and even credit scores, all without revealing their real name until necessary. This can dismantle the data silos that give big tech disproportionate power.
Global Interoperability and the Panopticon Problem
The World Economic Forum points out that previous identity solutions often fell into the “panopticon” trap, where a single-sign-on provider could track all user activity. Decentralized identity, combined with zero-knowledge proofs, finally offers a way to break that surveillance model. Cross‑border frameworks like eIDAS 2.0 and the NIST Digital Identity Guidelines are laying the regulatory groundwork for global acceptance.
“Blockchain-powered decentralized digital ID provides privacy-enhancing capabilities unlike current centralized systems more vulnerable to personal data exploitation and massive data breaches.” – Brett McDowell, Adviser, Hedera, via World Economic Forum
| Feature | Traditional Identity System | Blockchain Digital Identity |
|---|---|---|
| Data Control | Central authority (government, company) | User holds own credentials in wallet |
| Privacy | Full PII often exposed | Minimal disclosure via ZKPs |
| Security Model | Honey‑pot database targets | No central repository; individual encryption |
| Interoperability | Siloed per service | Universal via DIDs and VC standards |
| Breach Impact | Millions of records exposed | Limited to single shared attribute |
| User Experience | Multiple passwords, repetitive verification | Single wallet, drag‑and‑drop sharing |
Ready to build the future of digital identity? Apply to the Genesis Cohort at digitalblockchains.com and join the next wave of decentralized infrastructure builders.
Frequently Asked Questions
What is blockchain digital identity?
Blockchain digital identity is a system where personal identifiers are managed through a decentralized network, giving users ownership of their credentials. It uses DIDs and verifiable credentials to enable secure, privacy‑preserving identity verification without central authorities.
How does self‑sovereign identity relate to blockchain digital identity?
Self‑sovereign identity (SSI) is the core model for this technology. It means individuals control their identity data, deciding what to share and with whom, without relying on a central issuer. The blockchain provides the underlying trust infrastructure for SSI.
Is personal data stored on the blockchain?
No, personal identifiable information (PII) is never stored on the blockchain. Only cryptographic proofs (hashes) are written to the ledger, while the actual data remains encrypted in the user’s digital wallet. This prevents data breaches from exposing raw identity data.
What are the main benefits of using blockchain for digital identity?
The key benefits include enhanced privacy through minimal data disclosure, improved security by eliminating central honeypots, reduced verification costs and time, and true data portability. It also addresses the identity exclusion faced by over 1.1 billion people globally.
What are the leading standards for blockchain digital identity?
The primary standards are the W3C Decentralized Identifiers (DIDs) specification and the Verifiable Credentials (VC) data model. These ensure interoperability across different networks and identity providers. Additional protocols like OIDC4VC facilitate web integration.
Can blockchain digital identity be combined with existing enterprise IAM?
Yes, it can be phased in alongside existing systems. Many organizations use bridges that federate OAuth/OpenID Connect with DID‑based authentication. This allows gradual migration without abandoning current investments.